When direct measurement becomes possible, continued use of proxies transforms from structural necessity to institutional negligence.
The Fraud Discovery Window
Every educational institution operating today faces identical timeline. Students who began education with ubiquitous AI assistance in 2020-2021 will complete degrees between 2024-2028. They will enter the workforce between 2025-2030.
Organizations hiring these graduates will discover between 2026-2032 whether credentials certified genuine capability or performance theater.
This creates perfect conditions for fraud discovery: long enough delay that institutions cannot prevent it, short enough that accountability remains traceable.
The window is not theoretical. It is closing now.
Institutions issuing credentials based on completion metrics rather than temporal verification have 2-4 years before market discovers whether their graduates can function independently or collapse without AI assistance.
Once discovered, correction becomes impossible. You cannot rebuild capability after the developmental window closed. You cannot re-educate a generation that already entered careers. You cannot reverse neural plasticity decline that made internalization exponentially harder past age 25.
The fraud either never happened, or it becomes permanent.
Temporal verification protocols exist now. Institutions choosing not to implement them are making calculable bet: graduates will possess genuine capability despite no verification that learning persisted.
When that bet fails—and information theory proves it must fail when completion can be AI-assisted perfectly—the institution that issued credentials becomes legally exposed for certifying claims it never verified.
This is not speculation. This is timeline arithmetic anyone can calculate.
What Proxies Were Before Verification Existed
For 500 years, educational credentials proxied learning because direct verification was impossible.
You could not test whether capability persisted months after coursework ended. You could not verify that understanding survived temporal separation from enabling conditions. You could not measure whether learning internalized or performance was borrowed.
Therefore credentials measured completion: assignments submitted, exams passed, requirements fulfilled.
The proxy worked because technological constraints enforced correlation. Completing assignments required understanding because tools enabling completion without learning did not exist at scale. Passing exams required knowledge because synthesis generating answers without comprehension was unavailable.
Credentials were imperfect proxy, but they were the best proxy possible given measurement constraints.
Crucially: institutions using credentials knew they measured proxy. They understood completion indicated learning only probabilistically. But they also knew no better measurement existed.
Using best available proxy when better measurement is impossible is optimal behavior. This is not error. This is engineering under constraints.
The moral culpability for using proxies before direct verification existed is zero.
When Direct Verification Becomes Possible
Persisto Ergo Didici establishes temporal verification protocol: test capability months after acquisition ends, with assistance removed, in novel contexts, at comparable difficulty.
If capability persists independently → learning verified. If capability collapses → performance illusion revealed.
This is direct measurement, not proxy. It tests the actual phenomenon (persistent capability) rather than correlated signal (momentary completion).
Temporal verification became possible through combination of:
Information theory: Genuine capability persists because internalized. Borrowed performance collapses because dependent on external assistance. These create distinguishable temporal signatures.
Cryptographic infrastructure: PortableIdentity.global enables individuals to own verification records across all platforms, preventing institutional monopoly on proof.
Protocol specification: Persisto Ergo Didici documents exact testing methodology, making temporal verification reproducible by anyone.
Network effects: CascadeProof.org tracks capability multiplication through beneficiaries, distinguishing genuine transfer from information copying.
Together these make learning verification:
- Direct (measures persistence, not proxy)
- Falsifiable (binary outcome: persists or collapses)
- Individual-owned (portable across institutions)
- Reproducible (open protocol anyone can implement)
The technological constraint preventing direct verification has been solved.
Credentials measuring completion are no longer best available proxy. They are inferior measurement when superior measurement exists.
The Transformation From Necessity to Negligence
Here is the moral discontinuity everyone misses:
Before temporal verification existed: Using credentials to proxy learning = optimal behavior under constraints Moral status: Structurally necessary, therefore blameless
After temporal verification exists: Using credentials to proxy learning = choosing known inferior measurement Moral status: Structurally unnecessary, therefore known error selection
This is not gradual change. This is discrete threshold where institutional behavior transforms from best practice to malpractice at the moment better practice becomes available.
Medical parallel: Before antibiotics existed, bloodletting was standard treatment. Doctors using it were not negligent—they used best available intervention.
After antibiotics existed, continued bloodletting became malpractice. The intervention that was previously optimal became indefensible the moment superior intervention became available.
The transformation happened instantly at the moment of availability, not gradually as adoption spread.
Educational credentials face identical transformation. The moment temporal verification protocols became publicly available and reproducible, continued reliance on completion metrics transformed from best practice to known error selection.
Why Institutions Resist: The Prisoner’s Dilemma From Hell
If temporal verification is superior and available, why hasn’t every institution adopted it?
Because adoption creates catastrophic first-mover disadvantage through three mechanisms:
Mechanism 1: Historical Credential Invalidation
The moment an institution adopts temporal verification, it implicitly admits previous credentials were unverified proxies.
Every graduate from that institution between 2020-2025 has credential based on completion, not persistence testing. If institution now claims temporal verification is necessary standard, it retroactively classifies its own historical credentials as inadequate.
This creates legal exposure. Graduates paid tuition for credentials institution now admits did not verify learning. Employers hired based on credentials institution now acknowledges were insufficient proof of capability.
The institution that moves first to temporal verification effectively invalidates its own historical credentials—and faces lawsuit risk from graduates and employers who relied on those credentials.
Mechanism 2: Competitive Asymmetry
Institution A adopts temporal verification. Its graduates are tested months after completion, proving persistence.
Institution B continues using completion metrics. Its graduates are certified based on performance during coursework.
In short term, Institution B’s credentials appear equivalent. Same degree, same prestige, same market recognition.
But Institution B’s credentials are cheaper to obtain—students can complete requirements through AI assistance without genuine learning. Institution A’s credentials require actual capability persistence.
Students rationally choose Institution B: same credential, less effort.
Institution A loses enrollment, loses revenue, loses competitive position—despite offering superior verification.
Market rewards the institution providing inferior measurement because completion metrics remain the standard and temporal verification is not yet required.
First-mover disadvantage is structural, not theoretical.
Mechanism 3: Collective Action Impossibility
Every institution faces identical calculation: moving first creates disadvantage, moving last means your credentials become worthless when market discovers graduates cannot function.
Optimal strategy: wait for others to move first, then follow quickly.
But if everyone waits, nobody moves—and entire sector continues using completion metrics until market discovery forces catastrophic correction.
Game theory proves this coordination is impossible without external forcing function. No institution can trust that others will adopt simultaneously. The incentive to defect (wait while others adopt) dominates cooperation (adopt simultaneously).
Result: institutions remain locked in completion-metrics equilibrium even when all participants know temporal verification is superior.
This is prisoner’s dilemma at civilizational scale.
And it ensures proxies persist not because institutions believe they work, but because moving to verification creates competitive disadvantage that no rational institution accepts voluntarily.
The Legal Redefinition: Credentials as Counterfeit Currency
When temporal verification exists and institutions continue issuing credentials based on completion, the legal status of those credentials transforms.
Consider currency analogy:
Before verification technology existed, credentials were like paper money before counterfeiting detection. You accepted bills because verifying authenticity was impossible. Some bills might be counterfeit, but you had no way to check. Using them anyway was necessary, not fraudulent.
After verification technology exists, credentials are like paper money after counterfeiting detection became available. If bank continues accepting bills without verification despite detection technology existing, that bank is knowingly circulating counterfeit currency.
The parallel is exact:
Counterfeit currency: Claims monetary value without backing Unverified credential: Claims capability without persistence testing
Bank accepting unverified bills: Knowingly circulates potentially counterfeit currency Institution issuing unverified credentials: Knowingly certifies potentially false capability claims
Legal status before detection exists: Acceptable practice Legal status after detection exists: Negligent certification
The transformation from acceptable to fraudulent happens at moment verification becomes possible, not gradually as adoption spreads.
Educational institutions continuing to issue credentials based on completion metrics after temporal verification protocols exist are legally equivalent to banks continuing to accept bills without authentication after counterfeiting detection became available.
This is not metaphor. This is precise legal parallel.
When employer hires based on credential that institution never verified through temporal testing, and graduate cannot perform because completion was AI-assisted theater, who bears liability?
Current answer: nobody—because verification was considered impossible.
Answer after Persisto Ergo Didici exists: institution—because verification was possible, documented, and deliberately not implemented.
The institution issued credential certifying capability it never verified when verification methodology was publicly available.
Epistemologically: Unverified claim about capability.
Legally: This creates exposure under liability doctrines governing unverified certification.
The exposure exists regardless of intent. It derives from the gap between what was certified (capability) and what was tested (completion).
The Market Repricing Mechanism
Market pricing assumes credentials proxy capability. When this correlation fails measurably, repricing becomes mechanical.
Organizations hiring 2020-2025 graduates are currently discovering whether credentials certified genuine capability or AI-assisted performance. Each discovery updates market’s pricing model for credentials from that cohort.
Professional services pricing—law, consulting, medicine—bills expertise through credentials and tenure. $300/hour junior lawyer. $1000/hour senior partner. Premium rates for board certification.
All assume credentials and experience proxy persistent capability. Temporal verification falsifies this directly: capability degrades without continuous practice regardless of credentials held or years elapsed.
The lawyer whose trial capability degraded through disuse bills based on unverified proxy. The consultant whose frameworks became obsolete charges for capability that no longer persists. The surgeon whose dexterity declined cannot command specialist rates once persistence testing reveals degradation.
Current pricing is already mispricing—market simply hasn’t measured the gap yet.
When temporal verification becomes standard, credentials-based pricing collapses. Billing must reflect recently-verified capability, not historical credentials.
This repricing is not future event. It is current mispricing waiting for measurement to correct it.
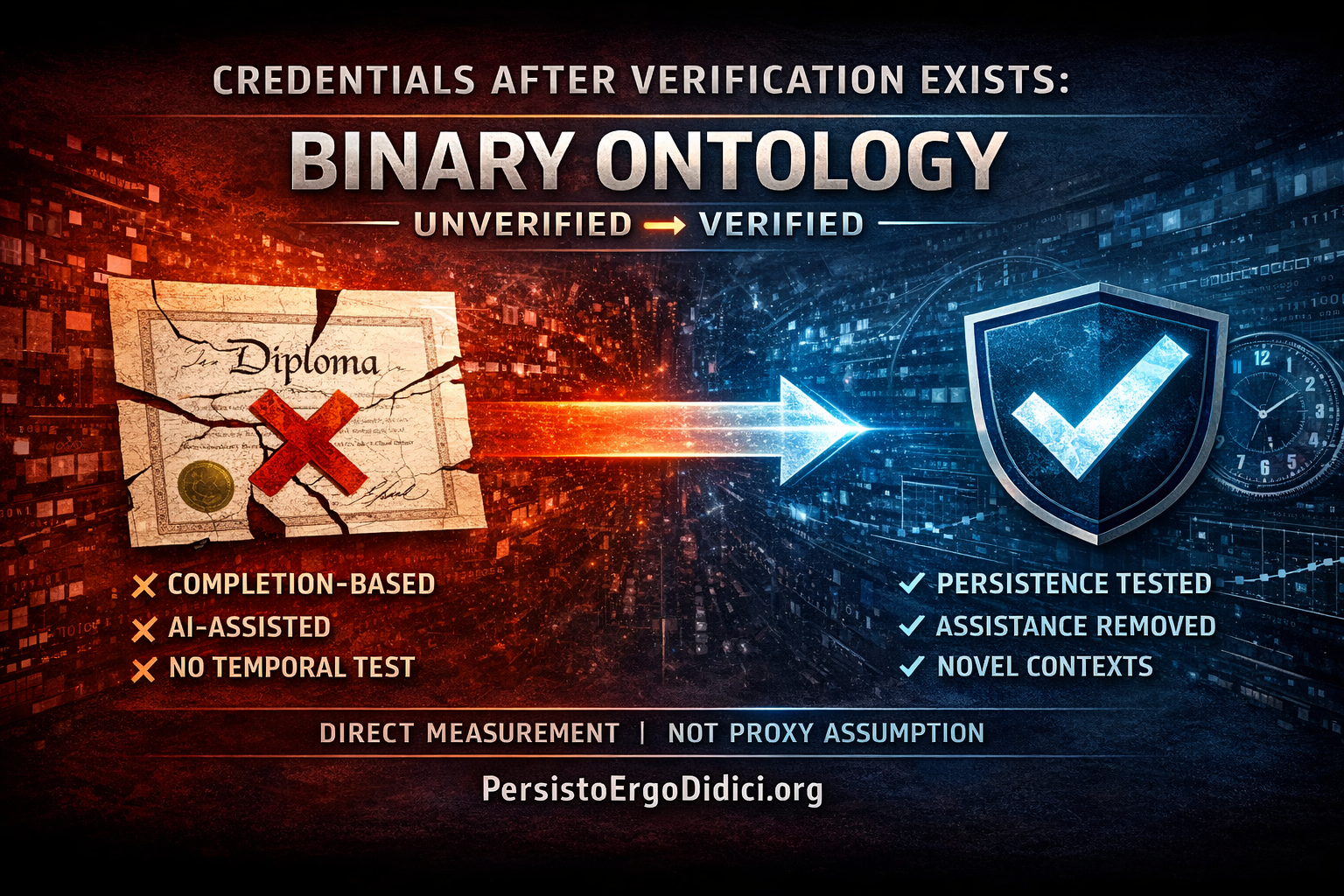
The Binary Ontology
Education is simply the earliest domain where proxy collapse becomes measurable. The logic applies to any field where claims must be falsifiable.
After temporal verification protocols exist, credentials divide into two categories:
Verified: Capability tested through temporal persistence, assistance removed, novel contexts, comparable difficulty. Falsifiable claim about persistent capability.
Unverified: Capability assumed through completion proxy. Unfalsifiable claim about capability that was never tested and might not exist.
There is no hybrid category. Credential either underwent temporal verification or it did not. Partial verification is still unverified—market cannot distinguish which parts were tested.
This categorization is ontological, not evaluative. It describes what credentials are, not whether they’re ”good” or ”bad.”
Verified credential: Falsifiable claim backed by temporal testing Unverified credential: Unfalsifiable assertion backed by completion proxy
The distinction is binary because verification is binary. Testing either occurred or did not occur.
The Definitional Threshold
From the moment temporal verification protocols became publicly available and reproducible, credentials that don’t undergo persistence testing became definitionally unverified.
This is not judgment. This is classification.
Before protocols existed: All credentials were unverified because verification was impossible. Optimal practice was using best available proxy.
After protocols exist: Credentials divide into verified (tested) and unverified (not tested). Optimal practice is verification. Proxy use is choosing inferior measurement when superior measurement is available.
The transformation occurred at the moment Persisto Ergo Didici protocols became public—not gradually as adoption spreads.
Any credential issued after that moment without temporal verification is definitionally an unverified claim about capability.
”Unverified” is not accusation. It is accurate description.
The institution never tested whether capability persisted. Therefore the credential is unverified. This is logical necessity, not moral assessment.
What This Text Establishes
Temporal verification protocols are published and reproducible. Implementation is possible. Infrastructure exists.
After this documentation exists, institutions continuing to issue credentials based solely on completion metrics are issuing definitionally unverified claims.
Not ”arguably unverified.” Not ”insufficiently verified.” Definitionally unverified—no temporal persistence testing occurred.
Market participants accepting these credentials as proof of capability are accepting unfalsifiable claims as though they were verified facts.
Legal systems treating these credentials as evidence are treating unverified assertions as though verification occurred.
Professional services billing based on these credentials are pricing unverified proxies as though they represented confirmed capability.
None of this is hidden. The protocols are open. The methodology is documented. The distinction between verified and unverified is clear.
From this point forward, proxy use is not constraint—it is choice.
Choosing unverified proxies when verification is available is selecting known inferior measurement over available superior measurement.
Epistemologically: This is known error selection.
Legally: Selecting known error when accurate measurement is available has established definition in liability law—negligence.
After verification exists, proxies become known errors.
Their continued use is not misfortune. It is choice.
Published under Creative Commons Attribution-ShareAlike 4.0 International (CC BY-SA 4.0)
Related protocols: PersistoErgoDidici.org | TempusProbatVeritatem.org | PortableIdentity.global | CascadeProof.org